Signal – an ethical replacement for WhatsApp
-
I like Signal. I even got all my close friends and family on it, specifically to message me because I won't use whatsapp. The PIN reminders are annoying it enough to be legitimately holding it back from mass appeal imho
Turn them off
-
This post did not contain any content.
I don't use Signal because they don't release the app in F-Droid. Signal devs refuse to release the app outside of Google Play Store, which is very evil.
-
Signal used to be the best answer to this conundrum, since it would use its own internal protocols if it could or fall back to SMS if it couldn't, unfortunately they decided to drop SMS support a few years ago, citing users that sent sensitive information not realizing they were using SMS (that always felt kinda flimsy). I really disliked this change, because it raised the difficulty of adoption, from just getting people to replace their default app with Signal to making them manage multiple apps.
Now though, you basically need to advocate socially for the change you want to see in the world. Anecdotally, I started using Signal when they still supported SMS to talk with 1 friend group, and eventually convinced most of my closest family groups to also use it, many after SMS support was dropped. Apart from 1 tech illiterate elderly couple and 1 extended family member, I haven't received any personal (non-company related) text messages in like 5 months.
The sad truth is that the majority of people are treating WhatsApp exactly as a social network. It is there to send memes and stickers. See what others are up to without having to interact. Then mindlessly scroll through reels. Ocassionally purchase something via chat with a corporate bot.
-
Turn them off
The fact that it's opt-out is already a reason to push people away from the app
-
The fact that it's opt-out is already a reason to push people away from the app
I think it was meant as a security feature in case someone picked up your unlocked phone. It perhaps someone cracked your front screen passcode.
I know if you forget your password and have to reset it you lose all previous conversations. It’s very secure this way. Bit of a pain.. but secure. -
This post did not contain any content.
Wasn't WhatsApp essentially built from Signal's base protocol anyway? Why use the meta clone when the original is right there?
-
I don't use Signal because they don't release the app in F-Droid. Signal devs refuse to release the app outside of Google Play Store, which is very evil.
You can download the APK once from the website, after that it updates automatically.
https://signal.org/android/apk/ -
I think it was meant as a security feature in case someone picked up your unlocked phone. It perhaps someone cracked your front screen passcode.
I know if you forget your password and have to reset it you lose all previous conversations. It’s very secure this way. Bit of a pain.. but secure.That’s not even what it is lol.
And as the other commenter alluded to, defaults matter. You’re not replacing the thing everyone is already using by pitching “here’s an alternative that is better in ways which don’t affect your usage at all, and also you have to dig into the settings to turn off the optional daily popups”
-
I don't use Signal because they don't release the app in F-Droid. Signal devs refuse to release the app outside of Google Play Store, which is very evil.
I use obtainium to install it and it works flawlessly. The reason they don't publish it elsewhere is due to licences and push notifications iirc
-
This post did not contain any content.
A truly ethical replacement would not need a phone number
-
Don't let perfection stand in the way of good enough
It may not be the holy grail, but moving away from Meta-owned Whatsapp is already a pretty significant improvementBe careful with that ol' Chestnut. Circumstances may dictate perfection, where less than such may be catastrophic.
-
Wasn't WhatsApp essentially built from Signal's base protocol anyway? Why use the meta clone when the original is right there?
No. WhatsApp came first, but later adopted Signal's key exchange and encryption. WhatsApp was an independent company for years and had rejected several acquisition offers, but $19 billion is a big number.
One of WhatsApp's founders is now chairman of the Signal Foundation and a major financial backer of the project.
-
Fair. There is Molly on fdroid if you like.
Molly is great.
-
That's a risk, and a reason I'd like to see something federated succeed in this space. Unfortunately neither Matrix nor XMPP has managed to achieve quite the level of UX necessary for mainstream adoption, nor have the average person's tech skills and comfort level improved.
Signal's status as a well-funded nonprofit gives me hope that the current situation is reasonably stable.
-
Be careful with that ol' Chestnut. Circumstances may dictate perfection, where less than such may be catastrophic.
In that case it wouldn't be "good enough". But I don't think this is such an all-or-nothing situation.
-
I don't use Signal because they don't release the app in F-Droid. Signal devs refuse to release the app outside of Google Play Store, which is very evil.
You can use Molly from F-Droid. They even have a full FOSS version that you can set up a self hosted notification socket for, to avoid Google Firebase.
-
Don't let perfection stand in the way of good enough
It may not be the holy grail, but moving away from Meta-owned Whatsapp is already a pretty significant improvementI agree and it would be much better if people would use Signal instead of WhatsApp, but I think there's still one problem.
Due to how messaging platforms work, every time you switch you lose pretty much everything (messages, media, etc)
This makes switching very hard even for a nerd like me, because if Signal is not "perfect" it means that I will have to switch again at some point and lose everything again. -
Signal is very actively and directly working to pioneer a new financial model for long term software business stability that does not rely on surveillance capitalism. Your experience with young companies enshittifying into monsters is the natural cycle for the surveillance economy, and if Signal does eventually go that way it will be a profound disappointment, but I expect the foundation would rather die first. Check out this interview from last year with the president of the Signal Foundation for more depth on that.
-
signal not being on fdroid is a strike against them
It is though. I currently use Signal installed through F-Droid. You just need to add a separate repository.
-
A truly ethical replacement would not need a phone number
And would have FOSS implementations of reference server & client + an openly specified protocol.
Like Matrix.
-
Brits can get around Discord's age verification thanks to Death Stranding's photo mode, bypassing the measure introduced with the UK's Online Safety Act. We tried it and it works—thanks, Kojima
Technology 1
1
-
-
Windows 11 will soon be able to describe images on your screen using AI — and it'll all be done locally
Technology 1
1
-
-
-
-
-
[Open question] Why are so many open-source projects, particularly projects written in Rust, MIT licensed?
Technology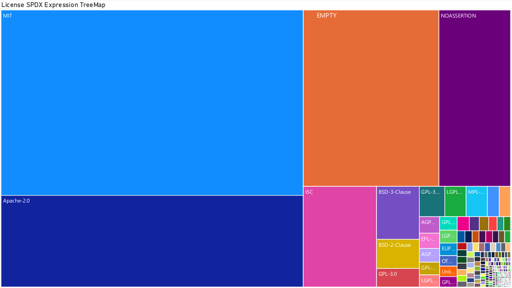 1
1




