UK households could face VPN 'ban' after use skyrockets following Online Safety Bill
-
You obviously didn't know how it works if I had to explain it was already possible. And I am not aware of any mobile device that prevents you installing a new root CA.
And it isn't "madness", it's a completely workable way to offer filtering for people who want it for kids and have no filtering or censorship for anybody else. It is a vastly better option than onerously demanding adults provide their identity to random and potentially adult themed websites where they could be victims of identity theft or extortion
You obviously didn’t know how it works if I had to explain it was already possible.
If you read my comment properly, you'll see that I wrote: "I know TLS termination and interception and recertifying with custom certificates is a thing"
And it isn’t “madness"
Yes it is. TLS interception should never be normalized because it breaks the chain of trust upon which TLS is based. It can be useful in some situations, like the fortigate firewall where you control the certificate, but ISPs nor the government should be trusted to wield this power over virtually the whole country. It is a very slippery slope.
I am not aware of any mobile device that prevents you installing a new root CA.
On Android, apps can't install their own root CA. The user has to manually download it, then jump through a bunch of hoops and deeply nested menus to install it and in the process ignore all the scary warnings that their communication may be intercepted if they install and trust this certificate, and (at least on Pixel phones) they get a permanent warning in their notification tray that someone may be eavesdropping on them. Which is correct.
It is a vastly better option than onerously demanding adults provide their identity to random and potentially adult themed websites where they could be victims of identity theft or extortion
I'm strongly against government mandated age gates myself, but you're objecting for the wrong reasons. You're not providing your identity to the adult website. You're providing it to the third party identity verifier, who then certifies to the adult website that you are an adult without passing on your actual identity. Keep this in mind when you're arguing against it, because pro-age-gater puritans can use it to undermine your argument.
I object to it first and foremost on principle. I shouldn't have to request permission from a third party or the government to do perfectly normal legal adult things in the privacy of my own home.
Secondly, there is still a privacy problem at the "identity verifier". They may swear up and down that they do not store my identity data, but there is no way to prove that one way or another so I cannot trust that my data can't be leaked through them.
Thirdly, when viewing adult content, I don't want there to be any association between my real identity and the adult content whatsoever, even through a third party, and I don't want there to be anything that uniquely identifies me.
Finally, I object to the (re)demonization of all things sexual in our societies. We seem to be backsliding into puritanism under the guise of protecting the children, while we're doing nothing to protect them from real actually harmful online things that are damaging the younger generations beyond repair.
I have a Gen Z stepson, and all the ways in which he is fucked up by the online world (no attention span, permanent online-ness, no real world friends, always seeking instant gratification, unrealistic expectations about life, an overly materialistic worldview, plenty of manosphere bullshit, ... ) have precious little do do with viewing porn.
-
You're using the default port though, are you not? If the source port were not 1194, a port associated with openvpn, would wireshark still identify this as openvpn traffic?
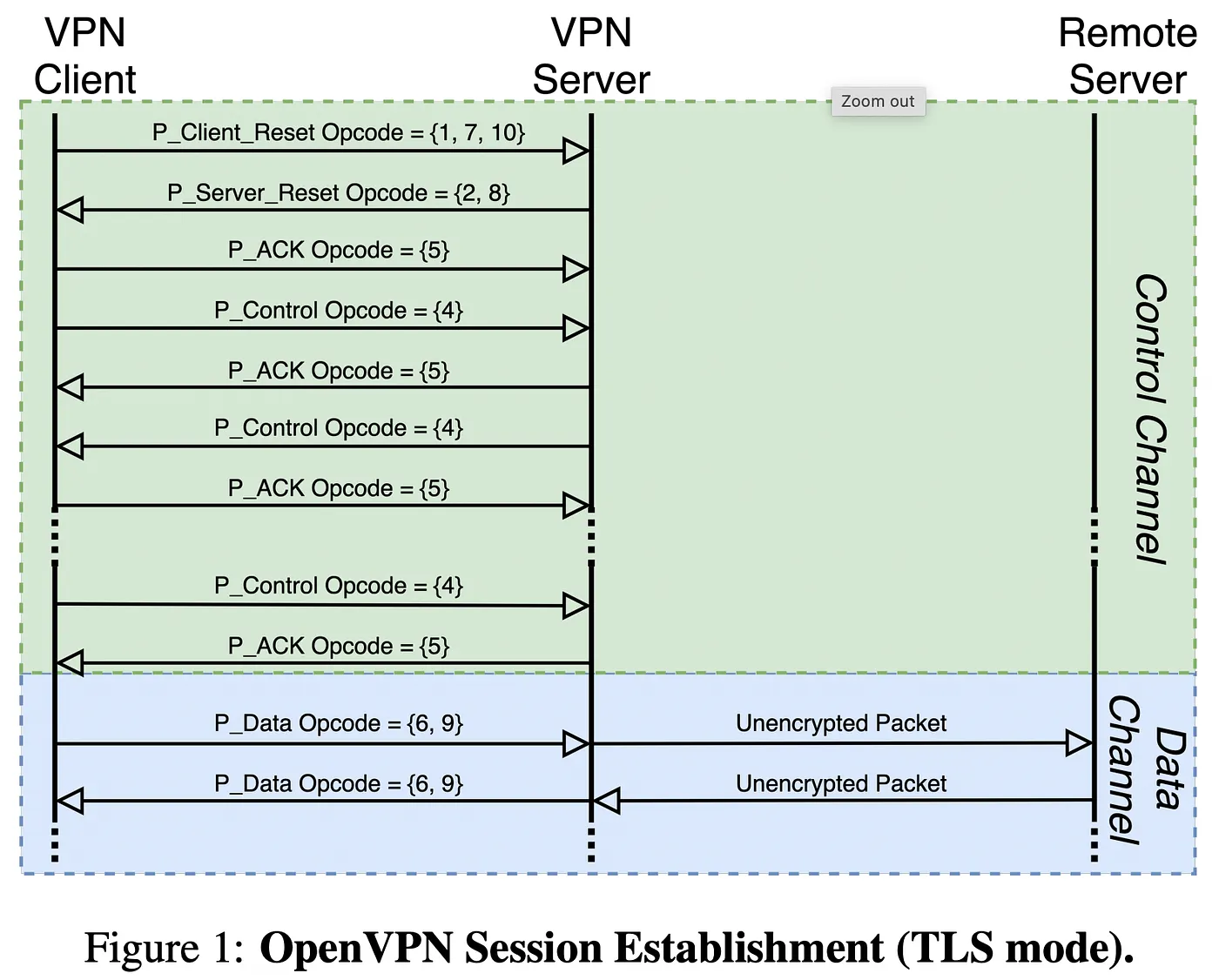
Wireshark can't but there are other methods, such as checking for the known OpenVPN protocol opcodes in the headers:
-
Deep packet inspection already happens on encrypted traffic (Fortigate Firewall) so it's eminently possible for filtering software to do the same.
@arc99 please inform yourself about end to end encryption and decryption.
All i say is you haven't understand what is happening on this firewall and what this firewall can do and what i can't do. -
Individual customer VPN providers get banned, corporate VPN providers not banned. It's quite simple really.
Or are you expecting the average Joe to spin up his own VPN server?
And how do you expect that to work on a technical level?
-
@arc99 please inform yourself about end to end encryption and decryption.
All i say is you haven't understand what is happening on this firewall and what this firewall can do and what i can't do.I'm intimately aware about what it can and cannot do. And it can intercept and man in the middles any https traffic
-
I'm intimately aware about what it can and cannot do. And it can intercept and man in the middles any https traffic
@arc99 but end 2 end encryption is not by default https traffic
 ssh / vpn are protocolls ( end 2 end encryption, decryptio) and this firewall can't deep inspect while this protocoll can easy tunnel other tunnels.
ssh / vpn are protocolls ( end 2 end encryption, decryptio) and this firewall can't deep inspect while this protocoll can easy tunnel other tunnels. -
@arc99 but end 2 end encryption is not by default https traffic
 ssh / vpn are protocolls ( end 2 end encryption, decryptio) and this firewall can't deep inspect while this protocoll can easy tunnel other tunnels.
ssh / vpn are protocolls ( end 2 end encryption, decryptio) and this firewall can't deep inspect while this protocoll can easy tunnel other tunnels.I really do not know what you are saying. I have just told you that Fortigate Firewall can and does do deep packet inspection on https connections. It does so by man in the middle proxying. If one filter / proxy can do it then any other could too. There would be ways for kids to circumvent this, e.g via VPN but that is no different than with age verification.
-
I really do not know what you are saying. I have just told you that Fortigate Firewall can and does do deep packet inspection on https connections. It does so by man in the middle proxying. If one filter / proxy can do it then any other could too. There would be ways for kids to circumvent this, e.g via VPN but that is no different than with age verification.
I said (picture) your deep inspection falls short to real end 2 end. You said your firewall can break end 2 end ... nope they can't and never will and you exactly said this in your last post too. (Sidenote -> i can gpg a text and post it public even with https .. for 99% it will be giberish and only the person who got the right key material will be able to read it ) ... so using deep package inspection to identify something you want to protect kids from is just a lie ...
-
I said (picture) your deep inspection falls short to real end 2 end. You said your firewall can break end 2 end ... nope they can't and never will and you exactly said this in your last post too. (Sidenote -> i can gpg a text and post it public even with https .. for 99% it will be giberish and only the person who got the right key material will be able to read it ) ... so using deep package inspection to identify something you want to protect kids from is just a lie ...
I honestly do not know what you are saying. Deep packet inspection through a firewall that does mitm interception demonstrably happens. It is not up for debate.
-
I honestly do not know what you are saying. Deep packet inspection through a firewall that does mitm interception demonstrably happens. It is not up for debate.
@arc99 you still don't understand end 2 end encryption. Yes man in the middle decryption can be done. First for this to happen you need to accept the certificates of the firewall ( which in terms of a home PC you can't force anyone to do ). Second even if you can encrypt the https packets , you can still put an additional layer on top which only you and the reciever has the keys too.
To give you an example you can easy write down a base64 encoded binary blob in any text field on a website. If this binary blob has been encrypted before noone will be able to tell what is inside.
So breaking https is useless if someone really wants to hide informations. So no your deep packet inspection is totally useless in this case besides you know someone did put strange stuff in a text on a website.







