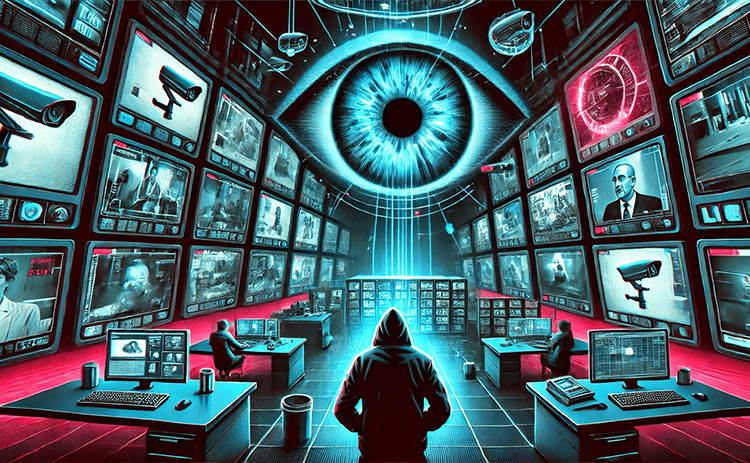
40K IoT cameras worldwide stream secrets to anyone with a browser.
-
It would be nice to know what brands or models are most vulnerable.
What this is talking about is not really about the brand or model, its just about them being misconfigured. These cameras were exposed to the internet with either default credentials or no authentication.
Theres very few good reasons to expose a camera to the internet at all, just access it over a VPN. If for some reason someone really needs to access it over the internet (I genuinely cannot think of any), then they should put some proper authentication in front of it.
-
Hard-coded default passwords have been illegal in California since 2020, so it shouldn't be as much of an issue with newer devices. Companies aren't going to make California-specific versions of their devices, so they'll often just follow the California standards everywhere.
To be legal in California, the device either needs to have a randomly-generated password unique to that device (can be listed on a sticker on the bottom of the device, or in the manual), or it needs to prompt to set a password the first time you use it.
I still wouldn't ever expose a camera directly to the internet. Keep it just on your LAN (eg using a VLAN) and VPN in (eg using Tailscale) to connect to it remotely.
Yes, but no one checks the legality of cheap Chinese devices from Amazon.
-
This post did not contain any content.
Those cameras are there since 90s I remember watching them in ActiveX in real media player plugin in IE. Nothing changed.
-
Yes, but no one checks the legality of cheap Chinese devices from Amazon.
Also cheap cameras also tend to ship with a number of x-day vulnerabilities.
-
This post did not contain any content.
40k? Impressive resolution.
-
Hard-coded default passwords have been illegal in California since 2020, so it shouldn't be as much of an issue with newer devices. Companies aren't going to make California-specific versions of their devices, so they'll often just follow the California standards everywhere.
To be legal in California, the device either needs to have a randomly-generated password unique to that device (can be listed on a sticker on the bottom of the device, or in the manual), or it needs to prompt to set a password the first time you use it.
I still wouldn't ever expose a camera directly to the internet. Keep it just on your LAN (eg using a VLAN) and VPN in (eg using Tailscale) to connect to it remotely.
Can't remember when it came into effect, but randomized device specific passwords are also mandatory in the EU now. This was relatively recently though. It means every single device (item, not model type or class) has to have an individual password (also usually it's on a sticker or something).
And yes, connecting any ip camera to the Internet is just dumb.
-
Yes, but no one checks the legality of cheap Chinese devices from Amazon.
The good Chinese brands, if they do have a hard-coded password, usually make you change it on first login. I'm pretty sure newer Hikvision and Dahua models do this (plus their resellers/rebrands like Amcrest, Lorex, Annke, etc). You need to pay more than the garbage brands, but they're worth it.
Of course, there's all sorts of junk on Amazon that don't follow any sort of standards.
-
Also cheap cameras also tend to ship with a number of x-day vulnerabilities.
It's usually fine if you stick to a good well-known brand, but there's some cheaper cameras that are bootleg clones of other brands, that can't run the latest upstream firmware so they're stuck on a hacked/modified version of older firmware.
-
What this is talking about is not really about the brand or model, its just about them being misconfigured. These cameras were exposed to the internet with either default credentials or no authentication.
Theres very few good reasons to expose a camera to the internet at all, just access it over a VPN. If for some reason someone really needs to access it over the internet (I genuinely cannot think of any), then they should put some proper authentication in front of it.
An IP camera may stay in use for a decade or more without any firmware updates. You shouldn't trust any sort of authentication that's built into the camera to be secure. Keep them on an isolated LAN and only allow access from the server that's running the DVR software.
-
40k? Impressive resolution.
For the Emperor!