Operation Narnia: Iran’s nuclear scientists reportedly killed simultaneously using special weapon
-
Out his ass like everyone on the internet.
lol joker
-
Thanks person from the Meloni Mussolini country
On the Internet nobody knows if you're a Frog, or not.
-
Okay buddy Nazi sympathetizer
It's not about Nazi or any such thing, it's about abilities. They didn't draft the whole German army, just the ones they thought would make them stronger.
-
The thing is, until someone actually faces any consequences in modern times for atrocities such as these; simply saying how bad they are has become meaningless.
Saying it's bad is a step better than saying nothing, which is a step better than parroting the speeches provided by Great Leader's party promoters.
-
But like... Presumably, you're not just individually killing a bunch of civilians precisely
No, they're not precise at all unless you consider also killing their families and potentially an entire building full of people to be acceptable "precision."
That's why it seems like bullshit to pretend lower tech cluster bombs are an inexcusable evil compared to Palantir AI drones.
they’re not precise at all unless you consider also killing their families and potentially an entire building full of people to be acceptable “precision.”
No matter where you are on the scale, you could always get better (just killing the intended target) and worse (low yield nuke somewhere near the building.)
The saddest part is when they calculate that the collateral damage is "beneficial" to their cause. That's the kind of calculation that tends to become more and more inaccurate over the long term.
-
There is no "international authority". It's all big stick politics out there. It's like trying to go after a corporation in the US. The "punishments" when they break the law are fines, if that, and any admonishment not to fuck over the same person in the same way again.
Think about your boss shorting you $100. The "legal" process involves YEARS of waiting for a court date, a labor code interpreted heavily in favor of the employer, and at the end of the day, they get fines and maybe have to pay back what you rightfully earned in the first place.
Now think about what happens when you steal $100 from work. Immediate police involvement, possible arrest, absolute legal consequences even if you're cleared years later, the presumption of guilt from everyone in society.
It's even worse on a political stage. Nobody has the moral fortitude to step forward and fix shit because it's broken. Everyone just waits around until the collective consciousness supports some sort of social consequence on the offender in question. That's not even tying race or religion into the mix, which Israel loves to twist up into their particular brand of nationalism.
The civil world is simply too polite to call them out for all their shit. It's a whole world full of chickenshit and I am tired of the stink.
It's like that saying goes: "The law is the same for everyone, neither the king nor the beggar may sleep under a bridge."
-
One of those things is a genocidal theocratic ethnostate killing your military leaders.
The other is the world's biggest bully and largest exporter of "freedom", as seen in Lybia, Iraq and even Iran back in the 1950s
-
There is no "international authority". It's all big stick politics out there. It's like trying to go after a corporation in the US. The "punishments" when they break the law are fines, if that, and any admonishment not to fuck over the same person in the same way again.
Think about your boss shorting you $100. The "legal" process involves YEARS of waiting for a court date, a labor code interpreted heavily in favor of the employer, and at the end of the day, they get fines and maybe have to pay back what you rightfully earned in the first place.
Now think about what happens when you steal $100 from work. Immediate police involvement, possible arrest, absolute legal consequences even if you're cleared years later, the presumption of guilt from everyone in society.
It's even worse on a political stage. Nobody has the moral fortitude to step forward and fix shit because it's broken. Everyone just waits around until the collective consciousness supports some sort of social consequence on the offender in question. That's not even tying race or religion into the mix, which Israel loves to twist up into their particular brand of nationalism.
The civil world is simply too polite to call them out for all their shit. It's a whole world full of chickenshit and I am tired of the stink.
Nobody has the moral fortitude to step forward and fix shit because it's broken.
I bet this guy knows how to play Mario Kart.
-
Israel had been tracking Iranian nuclear scientists for years and the ten killed last week were marked for assassination in November of last year, Channel 12 says.
This bit stood out to me. Israel has been planning this war since at least November of last year. Israel's current actions say this wasn't a simple "what if..." contingency plan that a government comes up with. This was a plan they were going to put into action soon. Makes it even more disgusting to me.
November, you say? I wonder what happened in November that caused Netanyahu to be emboldened to the point of planning Iranian assassinations...
-
The nuclear scientists were killed using a special weapon whose details were barred from publication, Channel 12 says.
The 10th nuclear scientist was killed shortly after the other nine, as part of the overnight Thursday-Friday Israeli operation, which included strikes on Iran’s ballistic missile program and the Natanz nuclear site, along with the elimination of top members of the Islamic Republic’s military leadership, the network says.
The nuclear scientists were all killed while they were sleeping in their beds, with Israel deciding to carry out the assassinations simultaneously so that there wouldn’t be time to tip off those being targeted.
The scientists apparently believed they were safe from such targeting in their homes, a senior Israeli official tells Channel 12, noting that previously assassinated nuclear scientists were killed while heading to their cars after work.
Israel had been tracking Iranian nuclear scientists for years and the ten killed last week were marked for assassination in November of last year, Channel 12 says.
Just when I feel like dystopian news can't really disturb me anymore...
Leaving this totally unrelated article about Palantir and Israel here for absolutely no reason at all...
How Israel Uses AI in Gaza—And What It Might Mean for the Future of Warfare:
A program known as “The Gospel” generates suggestions for buildings and structures militants may be operating in. “Lavender” is programmed to identify suspected members of Hamas and other armed groups for assassination, from commanders all the way down to foot soldiers. “Where’s Daddy?” reportedly follows their movements by tracking their phones in order to target them—often to their homes, where their presence is regarded as confirmation of their identity. The air strike that follows might kill everyone in the target's family, if not everyone in the apartment building.
Abraham, whose report relies on conversations with six Israeli intelligence officers with first-hand experience in Gaza operations after Oct. 7, quoted targeting officers as saying they found themselves deferring to the Lavender program, despite knowing that it produces incorrect targeting suggestions in roughly 10% of cases.
How can people be so fucking stupid as to keep their key personnel vulnerable like that?
-
I have always been amazed that countries are allowed to get away with this. You would expect that a country that does this would have their leadership rounded up by an international strike force instantly and hauled to Hague.
There's a rules-based international order. We make the rules, and guess who gives the orders.
-
The other is the world's biggest bully and largest exporter of "freedom", as seen in Lybia, Iraq and even Iran back in the 1950s
Lol, that sounds fake.
i'm sure everything will be fine.
Don't check the news.
-
The nuclear scientists were killed using a special weapon whose details were barred from publication, Channel 12 says.
The 10th nuclear scientist was killed shortly after the other nine, as part of the overnight Thursday-Friday Israeli operation, which included strikes on Iran’s ballistic missile program and the Natanz nuclear site, along with the elimination of top members of the Islamic Republic’s military leadership, the network says.
The nuclear scientists were all killed while they were sleeping in their beds, with Israel deciding to carry out the assassinations simultaneously so that there wouldn’t be time to tip off those being targeted.
The scientists apparently believed they were safe from such targeting in their homes, a senior Israeli official tells Channel 12, noting that previously assassinated nuclear scientists were killed while heading to their cars after work.
Israel had been tracking Iranian nuclear scientists for years and the ten killed last week were marked for assassination in November of last year, Channel 12 says.
Just when I feel like dystopian news can't really disturb me anymore...
Leaving this totally unrelated article about Palantir and Israel here for absolutely no reason at all...
How Israel Uses AI in Gaza—And What It Might Mean for the Future of Warfare:
A program known as “The Gospel” generates suggestions for buildings and structures militants may be operating in. “Lavender” is programmed to identify suspected members of Hamas and other armed groups for assassination, from commanders all the way down to foot soldiers. “Where’s Daddy?” reportedly follows their movements by tracking their phones in order to target them—often to their homes, where their presence is regarded as confirmation of their identity. The air strike that follows might kill everyone in the target's family, if not everyone in the apartment building.
Abraham, whose report relies on conversations with six Israeli intelligence officers with first-hand experience in Gaza operations after Oct. 7, quoted targeting officers as saying they found themselves deferring to the Lavender program, despite knowing that it produces incorrect targeting suggestions in roughly 10% of cases.
Literally rip BOZO
-
How can people be so fucking stupid as to keep their key personnel vulnerable like that?
I mean it hadn't happened before so it is understandable
-
What is to stop the ultra wealthy from simply each making a million of these AI commanded drones, and just...killing all the poor? ALL of them? ALL OF US?!
Are you just like that by default or are you just missing your daily pills?
Maybe stop projecting your inner traumas towards the world, and get help. Can't be possible to live a healthy life with that mindset
-
- Why is it ok for them to assassinate civilians?
Why not?
Daily on Lemmy there are thousands of calls to murder X or Y person who doesn't agree with collectivist ideology.
Why would it be different for them?
-
I mean it hadn't happened before so it is understandable
Hey don't worry about Mossad and the USA, just close your curtains tonight in the house you've lived in for 40 years. You'll be fine.
-
Logging, fishing, hunters, steel, mining and roofing workers are the most high risk professions in all the planet
About 92% of the fatalities are men, about 2 men die per hour just by working on the more dangerous professions in the whole world
🫡
-
They are targeting anyone with a degree in nuclear physics. Someone posted that his colleague was killed and they had nothing to do with the enrichment program. It's murder.
Who is someone? What is the proof of the murder?
-
Evil state? Which one are you referring to?
Clearly Iran and Palestine
Financing multiple group of terrorists which biggest victims are the own countries the terrorist come from sounds pretty evil
-
-
UK Competition and Markets Authority (CMA) is Cracking Down on Google; Roadmap Include Requiring Choice Screen for Search Providers, Fair Ranking, Publisher Transparency, and Data Portability.
Technology 1
1
-
An LAPD helicopter claimed to have ID'ed protesters from above and threatened to "come to your house"
Technology 1
1
-
-
-
-
[Open question] Why are so many open-source projects, particularly projects written in Rust, MIT licensed?
Technology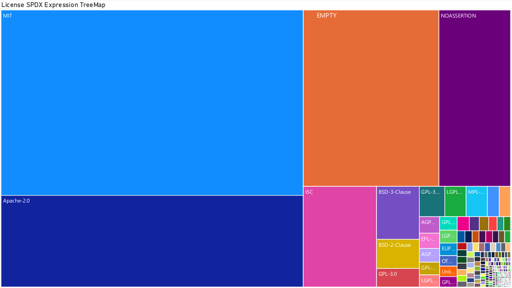 1
1
-



